Folder administrator access control defines the permissions that users or groups have to execute actions on folders and their contents. This mechanism is crucial for maintaining security and data integrity within a system. By granularly configuring access levels, administrators can ensure that only authorized individuals are permitted to read, change, or erase files and folders. This helps mitigate unauthorized access, data breaches, and potential system malfunction.
Common access control techniques include role-based permissions, where users are assigned roles with predefined permissions. Another technique is attribute-based access control (ABAC), which relies on user attributes, resource attributes, and environmental factors to determine permission.
Controlled Access Pathways
Controlled access pathways provide for the secure movement of people and through designated areas. These pathways often utilize a combination of physical barriers, such as fences and walls. Moreover, controlled access paths often integrate precisely located access portals. This contributes to a secure and regulated atmosphere by preventing breaches of security.
Entry Controlled Load Management
ANP Controlled Load Access refers to a strategy that mandates restrictions on the quantity of load that can be transmitted to an ANP platform. This method helps maintain system stability by controlling overloading on the assets of the ANP.
- Positive Outcomes of ANP Controlled Load Access include:
- Optimized system performance
- Minimized risk of outages
- Equitable distribution of resources among users
- Heightened security and resilience
Granular File System Permissions
In the realm of cybersecurity and system administration, fine-grained file system permissions represent a crucial mechanism for controlling access to sensitive data and resources. These granular permissions allow administrators to specify precise levels of authorization for individual users or groups, dictating which files and directories they can access, modify, and perform. By implementing such meticulous control over file system access, organizations can reduce the risk of unauthorized alterations, data breaches, and system compromise.
Strict Directory Access Management
Directory access management serves a critical role in safeguarding the confidentiality and integrity of your organization's valuable data. Implementing a secure directory access management system facilitates you to granularly control who has access to what data. This promotes that only permitted users can retrieve the information they need for their roles and responsibilities, while minimizing the risk of unauthorized access, data breaches, and other security concerns. A well-designed directory access management system incorporates a combination of authentication methods, such as multi-factor authentication and role-based access control, to fortify the security posture of your organization.
Implementing Robust Access Control Policies
Robust access control policies are essential/critical/fundamental for safeguarding sensitive data and maintaining the integrity of any system. These policies define who/which users/whom can access what/which/specific resources and under what circumstances/conditions/situations. Implementing such policies vías de acceso controladas involves a multifaceted approach that encompasses identifying/recognizing/determining user roles, assigning appropriate permissions, and enforcing multi-factor authentication to minimize the risk of unauthorized access.
Regularly reviewing/Continuously updating/Periodically auditing these policies is crucial/vital/indispensable to ensure they remain effective in the face of evolving threats. By adopting a proactive approach to access control, organizations can establish a strong security foundation and protect their valuable assets from potential breaches.
 Kirk Cameron Then & Now!
Kirk Cameron Then & Now!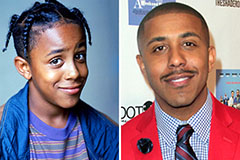 Marques Houston Then & Now!
Marques Houston Then & Now! Michael Jordan Then & Now!
Michael Jordan Then & Now! Nancy Kerrigan Then & Now!
Nancy Kerrigan Then & Now! Justine Bateman Then & Now!
Justine Bateman Then & Now!